Common social media security risks Unattended social media accounts It can be a good idea to reserve your brand’s handle on all social media channels, even if you don’t plan to use them all right away. For brands, the risk to privacy is higher because of the number of people who use social media in the office—for business and personal use. Using each network’s mobile app makes it easy to access social media accounts with just one tap. Train your staff on social media security best practices Even the best social media policy won’t protect your organization if your employees don’t follow it. Limiting access to your social accounts is the best way to keep them secure. Once you’ve decided who can post, use software like Hootsuite to give the right people the right account access. No one at Z-Burger saw the tweet before it was posted, since they had given the contractor the ability to publish directly to their account. This person should own your social media policy, monitor your brand’s social presence, and determine who has publishing access. Recent social media security threats. Maintain a good relationship with your company’s IT team so they can keep you informed of any new social media security risks they become aware of.

With the amount of information stored and shared online, social media security is more important than ever.
There’s no doubt social has made the world a more connected place. In most cases, that’s a good thing. But all those connections also create unprecedented access to people’s and business’ information. And that can be a very bad thing when hackers and scammers get involved.
Giving up social media is not a reasonable option. But neither is it reasonable to carry on as if social networks are always safe and secure. You need to take steps to protect your company against some of the most common social media security threats. Here’s where to start.
Common social media security risks
Unattended social media accounts
It can be a good idea to reserve your brand’s handle on all social media channels, even if you don’t plan to use them all right away. This allows you to maintain a consistent presence across networks, making it easy for people to find you.
But it’s important not to ignore the accounts you don’t use yet, those that you’ve stopped using, or those you don’t use often.
Idle social accounts can be the target of hackers, who could start posting fraudulent messages under your name.
Knowing the account is unmonitored, once they gain control, they could send anything from false information that’s damaging to your business to virus-infected links that cause serious problems for followers. And you won’t even notice until your customers start coming to you for help.
Human error
Everyone makes mistakes. In today’s busy world, it is all too easy for an employee to accidentally expose the company to threats online. In fact, 77 percent of respondents to the 20th EY Global Information Security Survey said that a careless member of staff was the most likely source of a cybersecurity threat.
Something as simple as clicking on the wrong link or downloading the wrong file could wreak havoc.
Bonus: Register for our upcoming webinar, “Build and Protect Your Brand on Social Media,” to learn everything you need to know about online reputation management—from potential risks to mitigation tactics (and tools).
Third-party apps
Even if you have your own social accounts on lockdown, hackers may be able to gain access through vulnerabilities in third-party apps that integrate with the big social networks.
For example, hackers gained access to the Twitter accounts of Forbes and Amnesty International using a flaw in the Twitter Counter app, used for Twitter analysis.
Phishing attacks and scams
Phishing scams use social media to trick people into handing over personal information (like banking details, passwords, or business information).
A recent social media scam involved false reports that the actor Rowan Atkinson had died. (The Mr. Bean and Blackadder actor is still very much alive.)
What looked like a video link actually directed users to a page that said their computer had been locked, with a phone number to call for support. Rather than a support team, the phone line connected to scammers looking for credit card numbers and personal information. Worse, the “support software” offered was actually a virus.
Filmmaker Tyler Perry recently posted a video to his Facebook account warning fans not to fall victim to giveaway scams using his name. He said his team has to shut down, “10, 20, 30 of these things” every day.

Imposter accounts
The number of fraudulent social support accounts doubled between the third quarter of 2016 and Q3 2017. Those accounts can target your customers, tricking them into handing over confidential information and tarnishing your reputation in the process.
Imposter accounts may also try to con your employees into handing over login credentials for corporate systems.
Malware attacks and hacks
Social media hackers are becoming more sophisticated. Hackers have gained access to big-name Twitter accounts, from Kylie Jenner and Mark Zuckerberg, to several HBO shows.
#Media Last night OurMine hacked HBOs social properties to show them why they need to hire them for corporate network security ???? #HBOhacked pic.twitter.com/zUOa15WGQO
Those hacks were fairly benign. Others are much more serious.
For example, hackers used a fake profile to connect with employees of targeted organizations, sharing a file that gave the attackers remote access to the victims’ work computers.
Privacy settings
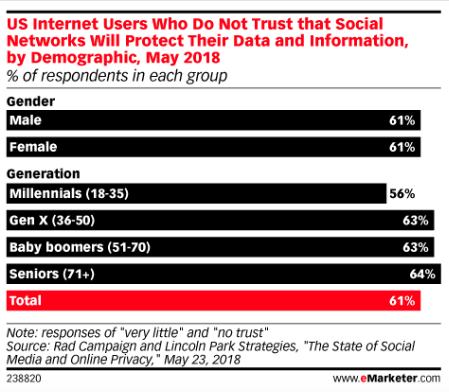
People seem to be well aware of the potential privacy risks of using social media. A recent survey found that nearly two-thirds of people have “very little” or “no” trust in social networks when it comes to privacy protection.
But those concerns don’t stop us from using our favorite social channels.
For brands, the risk to privacy is higher because of the number of people who use social media in the office—for business and personal use.
Unsecured mobile phones
Mobile devices are the most popular way to access social networks. Using each network’s mobile app makes it easy to access social media accounts with just one tap.
That’s great as long as your phone stays in your possession. But if your phone, or…

COMMENTS